Phishing emails, especially how to spot phishing emails pose a significant worry for business owners, and understandably so. With one out of every 99 emails being a phishing attempt and approximately 90% of data breaches originating from phishing, the stakes are high.
As businesses in various sectors acknowledge the growing threat of cyberattacks and bolster their cybersecurity measures, attackers are resorting to crafty tactics to breach defences.
In this article, we’ll dig deep into the intricate nuances of a phishing email. We’ll unveil its structure and provide you with the understanding required to spot and counter such deceitful endeavours.
Let’s examine the crucial components that aid in distinguishing between a legitimate email and a phishing scheme.
But What Exactly Is Phishing?
Phishing emails are cunning modes of communication crafted to deceive the recipient into divulging sensitive data or taking actions that could endanger the security of a network. The objective of a phishing attack is to earn the recipient’s confidence, thus gaining access to accounts, infiltrating a network, or disseminating malware. On occasion, a persuasive phishing scam or email might even result in transferring funds to the attacker’s account.
8 Most Common Indicators Of A Phishing Attempt: What To Look For
- Sender’s Address: Check the sender’s email address closely. Scammers often use slightly altered or fake email addresses that mimic legitimate sources.
- Urgent Language: Phishing emails often create a sense of urgency, pressuring recipients to take immediate action. Be cautious of emails that demand quick responses.
- Generic Greetings: Beware of emails that use generic greetings like “Dear Customer” instead of addressing you by name. Legitimate organizations usually personalize their communications.
- Suspicious Links: Hover over links without clicking on them to view the actual URL. Phishing emails may disguise malicious links with hyperlinked text that seems legitimate.
- Mismatched Branding: Look for inconsistencies in logos, branding, and design elements within the email. Cybercriminals might use altered images to imitate trusted organizations.
- Requests for Personal Information: Be cautious of emails requesting sensitive personal or financial information. Legitimate institutions never ask for such details via email.
- Spelling and Grammar Errors: Many phishing emails contain language mistakes. Legitimate organizations generally maintain higher standards of language and communication.
- Too Good to Be True: Be wary of emails promising incredible rewards or prizes. If an offer seems too good to be true, it’s likely a phishing attempt.
Let’s analyze the following example:
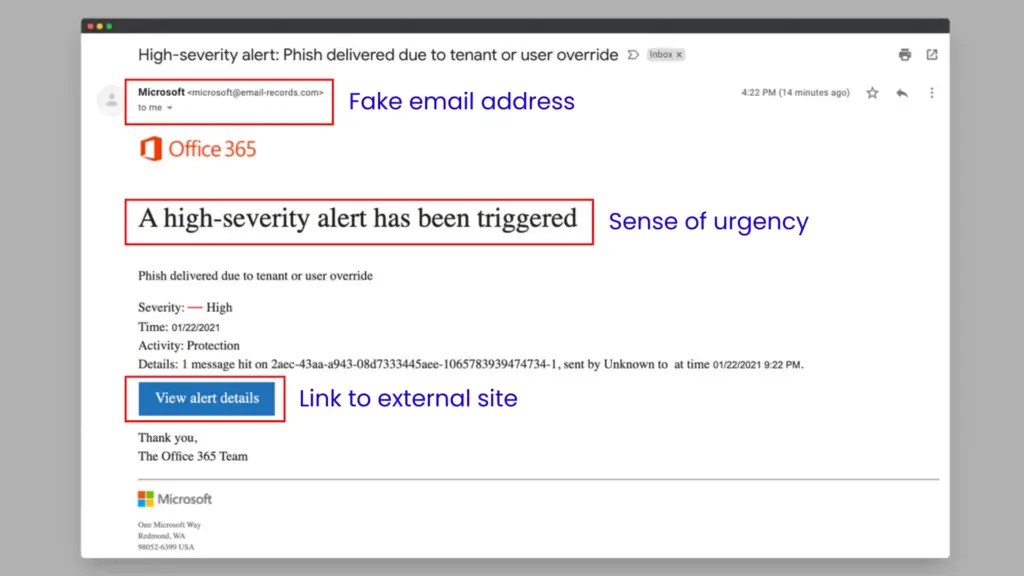
Email address: The email domain used is not from Microsoft (email-records.com)
Sense of urgency: The email was crafted to trick the user so that he/she believes that is suffering from a threat and clicks on the link.
Link: The email contains a link that will most likely redirect to a malware site.
Stay Informed – Free Resources Online
Similar to various other forms of cyberattacks, phishing emails are in a constant state of evolution. Thus, it is of utmost importance to continually engage in educational efforts to stay ahead of impending attacks.
By staying informed about the dynamic landscape of phishing assaults, you significantly enhance your ability to effectively detect and steer clear of them.
The following resources serve as valuable help in delving deeper into the realm of phishing emails, equipping you with the knowledge to identify and thwart their advances.
Recommended Online Resources And Materials
Empowerment through knowledge stands as a formidable defence against phishing emails. The silver lining lies in the presence of reputable institutions consistently updating their repository of resources to aid both individuals and enterprises in recognizing and evading the pitfalls of phishing emails.
Phishing.org extends a repository of tools for testing and discerning phishing attacks.
The Anti-Phishing Working Group (APWG) furnishes a conduit for corporations to report phishing assaults.
The Canadian Centre for Cyber Security extends complimentary cybersecurity resources, services, and tools aimed at mitigating cybersecurity risks, encompassing the realm of phishing threats.
How to stay protected from phishing attacks
Request Verification
Whenever you receive an email that requests sensitive information or urges you to take immediate action, verify its legitimacy. Use official contact information from the organization’s official website or directly contact the sender through a trusted method to confirm the request.
We recommend adopting a zero-trust security approach. Zero trust security starts with the assumption that everyone and everything is untrusted.
Beware of Suspicious Emails and Attachments
Be cautious of unsolicited attachments in emails from unknown senders or unexpected sources. Avoid opening attachments or clicking on links in such emails. Cybercriminals often use these tactics to spread malware or steal your personal data.
Look for Mistakes
Carefully review the email for any poor spelling, grammar, or formatting errors. Legitimate organizations usually maintain professional communication standards, while phishing emails may contain noticeable mistakes.
Resist the Temptation to Click on Links or Attachments
Even if an email claims to offer rewards, prizes, or urgent alerts, refrain from clicking on any embedded links or downloading attachments. Hover over links to see the actual URL before taking any action.
Similarly, a majority of links embedded within emails employ a button bearing hyperlinked text that describes an action like “Submit Payment”, “Update Account Details”, “Access Help Centre”, or “Modify Payment Method”.
Before clicking on any link, it’s wise to verify the intended destination. On a computer, hovering the cursor over the link reveals the destination address in a small bar. On a mobile device, holding down the link triggers a pop-up displaying the link.
A few extra tips:
Employ security software Configure the software to update automatically, ensuring it addresses any emerging security risks
Enable automatic software updates. These updates can provide essential defence against security threats.
Employ Multi-Factor Authentication across all your accounts
Certain accounts offer additional security by demanding two or more credentials for account access. This security method, known as multi-factor authentication, involves three categories of user credentials namely:
– Something you know, such as a passcode, PIN, or response to a security query.
– Something you possess, like a one-time verification passcode received via text, email, or from an authenticator app, or a security key.
– Something you are, encompassing traits like a fingerprint scan, retinal scan, or facial recognition.
Multi-factor authentication makes it harder for scammers to log in to your accounts if they do get your username and password.
Protect your data by backing it up.
Back up the data on your computer to an external hard drive or in the cloud. Back up the data on your phone, too.
Security Measures to Protect Against Phishing Attacks
Hackers strive diligently, but cybersecurity experts exert even greater effort. Preventing phishing emails from reaching employees’ inboxes is a significant challenge. Incorporating modern antiphishing software and email filters into cybersecurity measures is crucial. Robust security tools, often AI-powered, can identify and block malicious senders using existing data. The most potent defence against phishing employs a multi-layered strategy.
Enhanced Email Security: Prioritizing convenience, email often compromises security. Adjusting default settings, such as activating link protection and restricting email downloads, can bolster defences against phishing attacks. Robust email protection involves measures like login security, email encryption, spam filtering, fraud prevention, and comprehensive cybersecurity training for all staff levels.
Intrusion Detection and Response: While firewalls deter malware entry, the lack of post-entry prevention can enable phishing attacks to succeed. AI-driven detection and response systems recognize suspicious network activity, isolating threats swiftly to impede an attacker’s progress beyond the initial breach via email.
AI-based Network Detection and Response (NDR): NDR with AI relies on behaviour baselines to identify anomalous network actions. Alerts and potential threat quarantining enhance security. These tools are especially effective when genuine email accounts are compromised.
Steps to Take if You Suspect a Phishing Attack
Refrain from Engagement: As a priority, avoid interacting with the situation by refraining from clicking on any links or downloading attachments included in the questionable email. These actions could potentially jeopardize your security.
Confirm Authenticity: Thoroughly validate the sender’s email address and thoroughly examine the content for any indications of phishing, such as spelling errors, unusual URLs, or appeals for sensitive information.
Take Screenshots: Document the suspicious email by capturing screenshots that encompass the sender’s address, subject line, and any content that raises suspicion.
Forward the Email: Initiate a new email, attach the screenshots, and then transmit the questionable email to your organization’s IT department or the abuse department of your email service provider. Their contact details are typically accessible on their official website.
Use the “Report Phishing” Functionality: Many email service providers feature a “Report Phishing” or “Mark as Phishing” option. Employ this functionality to alert the email service provider about the malicious email.
Inform Anti-Phishing Entities: If you wish to take an additional measure, you can report the phishing email to anti-phishing entities like the Canadian Centre for Cyber Security via contact@cyber.gc.ca. These organizations monitor trends in phishing and undertake measures against cyber criminals.
Notify Your Institution: In case the email was received within a professional or business context, promptly notify your IT or cybersecurity team about the suspicious email.
What to Do if You’ve Clicked on a Phishing Link
If you’ve unintentionally clicked on a phishing link, there’s no need to panic. Here’s a guide on how to minimize any potential harm:
1. Disconnect from the Internet: Immediately sever your device’s connection to the Internet by disabling Wi-Fi or disconnecting the Ethernet cable. This action can halt further communication between your device and the attacker’s server.
2. Conduct a Malware Scan: Perform a thorough scan using your antivirus software to identify any potential malware that might have been downloaded or installed due to clicking the link.
3. Revise Passwords: Alter the passwords for all accounts you accessed via the phishing link. This encompasses email, social media, financial institutions, and other online platforms. Create robust, distinct passwords for each account.
4. Implement Two-Factor Authentication (2FA): If the accounts you utilized support it, activate two-factor authentication (2FA). This extra layer of security mandates a verification code in addition to your password.
5. Monitor Account Activity: Keep a vigilant watch over your accounts for any unusual transactions or activities. Should you detect anything suspicious, promptly inform the relevant service provider.
6. Notify Your Financial Institution: If you divulged financial or credit card information on a phishing site, urgently reach out to your bank or credit card company. Share the situation with them so they can monitor your accounts for unauthorized transactions.
7. Inform Contacts: If the phishing link was received through email, notify your contacts that your account may have been compromised. Cybercriminals often exploit compromised accounts to disseminate harmful content.
8. Report to Authorities: If the phishing incident encompassed financial fraud, identity theft, or other illicit activities, report the occurrence to your local law enforcement agency or pertinent cybercrime reporting entities.
9. Update Software: Confirm that your operating system, browsers, and security software are all up to date. Maintaining current software helps guard against known vulnerabilities.
10. Enhance Your Knowledge: Use this occurrence as an opportunity to educate yourself and others about phishing risks. Acquiring the ability to identify phishing emails and links can substantially decrease the chances of future attacks.
Remember, swift action can significantly mitigate the consequences of a phishing episode. Maintain vigilance and execute the necessary measures to safeguard your devices and accounts.




