In a world where our personal devices have become our constant companions, bridging the gap between work and play, it’s crucial to acknowledge the potential security risks that come with this convenience.
The reality is that cybercriminals have set their sights on mobile device users, launching attacks through devious means such as malicious apps and treacherous email attachments.
The consequences are far from trivial, as organizations face staggering financial losses, with stolen company data fetching hefty prices in the underground market.
According to the Cost of a Data Breach Report by IBM, The global average cost of a data breach in 2023 was USD 4.45 million, which represents a 15% increase over 3 years.
To safeguard against such threats, IT administrators face the ongoing challenge of balancing employee demands with security risks. The right Mobile Device Management (MDM) practices can be a formidable shield against mobile security threats and data breaches.
In this MDM security guide, we’ll explore 12 essential mobile device management (MDM) best practices.

Understanding Mobile Device Management Policy
In a dynamic and technology-driven work environment, where employees rely on various devices such as laptops, smartphones, and tablets, it’s crucial to balance productivity and security.
This is where the Mobile Device Management policy emerges as a key protagonist, safeguarding your company’s sensitive information and ensuring a robust defence against potential threats.
So, what exactly is an MDM policy? Simply put, it’s a set of rules and guidelines that govern the usage and protection of mobile devices within your organization.
It’s like a rulebook that helps you avoid cybersecurity threats, prevent theft, and thwart corporate surveillance attempts.
From laptops and smartphones to tablets and portable media devices, these tools demand strict measures to mitigate risks.
And it’s not just about your full-time employees; contractors, part-time staff, and anyone who can access company data through mobile devices must adhere to these policies.
When it comes to mobile device usage, there are three main categories to consider:
- Bring Your Own Device (BYOD)
- Company Owned/Business Only (COBO)
- Company Owned/Personally Enabled (COPE)
Each category brings its own challenges and intricacies that need to be addressed in your MDM policy to ensure comprehensive protection.
12 Essential Mobile Device Management Best Practices
These are the 12 essential practices for best Mobile Device Management that can help you establish a solid foundation to enhance the mobile device security of your organization.
1. Turn User Authentication On
When it comes to securing your company’s valuable information, you can’t afford to take any chances. That’s why turning on user authentication for all your own devices is essential.
By enabling screen locks and requiring passwords or PINs for access, you create an important barrier against potential theft or unauthorized access.
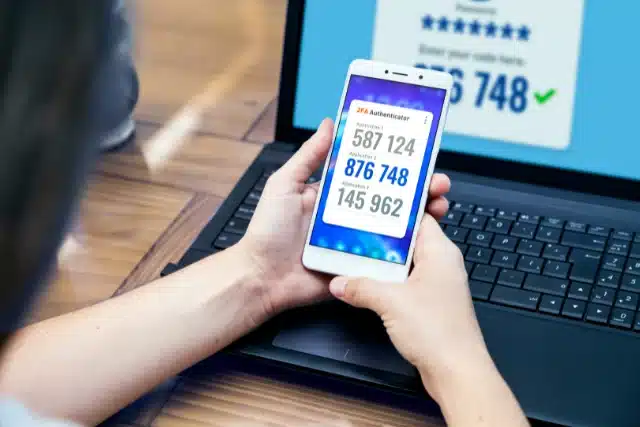
While biometric security options like Face ID and Touch ID offer convenience, they might not be foolproof. That’s where Multi-Factor Authentication (MFA) comes in.
To protect against the potential compromise of stolen mobile devices, your IT team must be able to remotely wipe devices, erasing sensitive data and mitigating the risk of unauthorized access.
2. Identify Mobile Needs
Choosing the right Mobile Device Management solution is crucial for effective device management. To avoid common pitfalls, assessing your team’s total mobility applications wants, and needs is important before selecting a MDM software.
Don’t make the mistake of choosing MDM software based solely on one department’s requirements. Consider factors such as the devices and operating systems you need to manage, the number of devices in your organization, and any specific MDM challenges you aim to solve.
By understanding your mobile needs, you can make an informed decision and find a MDM solutions that align with your organization’s requirements, ensuring seamless device management across your entire workforce.
3. Enable Risk-Based Access Policies
Managing mobile devices outside your direct control can be challenging. To mitigate risks, it’s recommended to implement risk-based access policies.
These policies grant or limit authorization based on user credentials and factors like the device used and its security posture.
Don’t hesitate to deny authorization if something doesn’t meet your security standards. It’s better to be cautious and protect your sensitive corporate data from potential breaches.
4. Whitelist, Blacklist, and Update Applications
Take control of the applications on your corporate devices or networks to enhance security and productivity. Create a whitelist of essential apps employees need for their tasks while blocking non-essential ones that pose potential risks.
This proactive approach ensures compliance with corporate security policies and minimizes the chances of unauthorized app usage.
Additionally, mandate regular updates for commonly used applications to address performance issues and patch any vulnerabilities. By actively managing your app ecosystem, you strengthen your Mobile Device Management strategy and safeguard your organization’s digital assets.
5. Bring-Your-Own-Device (BYOD) Policy
An efficient BYOD policy is essential to enhance your mobile security. So, what should you include? Here are some key elements to consider:
- Clearly outline which mobile devices are allowed on your corporate network—no room for ambiguity.
- Establish stringent security policies, mandating lock screens, biometric identification, and regular updates.
- Set clear expectations for acceptable usage, including apps, cloud services, and third-party software.
- Seamlessly integrate your BYOD policy with your acceptable use policy, leaving no room for uncertainty.
- Have a well-defined exit strategy to revoke access when employees swiftly part ways with the company.
6. Implement Strong Passwordless Authentication
Traditional passwords can be a headache. They’re hard to remember and prone to attacks.
When securing mobile devices, the immediate response is often to enforce strong passwords or employ multi-factor authentication tactics.
Eliminating passwords and relying on more secure factors like passcodes enhances mobile device security and eliminates common password-based attacks.
7. Utilize a Password Manager for Enhanced Security
Dealing with passwords can often be a cumbersome and frustrating task. Fortunately, password managers offer a reliable solution. Consider them as digital vaults, safeguarding your passwords with an exclusive master key accessible only to you.
By leveraging a password manager, not only do you ensure the security of your passwords, but you also benefit from the generation of robust, unique passwords.
This eliminates the need for predictable choices such as “password123.” But also ensure that all employees utilize secure passwords that are known only to them.
8. Use Cloud Security and Data Backup
Remember, your employee-owned mobile devices access cloud-based apps and services, increasing the risk of data loss. To stay ahead of potential threats, prioritize cloud security and data backup. Select a cloud platform that offers version history and roll-back capabilities.
Opt for a cloud platform that offers version history and consider a reliable cloud-to-cloud backup solution for added peace of mind. Backing up your files and data is crucial for easy restoration and uninterrupted access to critical information.
9. Automate to Save Time
Automation not only eases the burden on your IT team but also promotes top-notch security practices.
According to a recent Salesforce survey, a whopping 74% of IT leaders reported that process automation gave them back a valuable 30% of their time.
Whether you’re managing a handful or a mass of devices, or utilize mobile device management solution that automates report generation, sends alerts for policy violations, and simplifies device lock and data wipe tasks.
10. Enforce Updates
Keeping your software updated is not just good practice—it’s essential for a secure IT environment. Neglecting to enforce software updates puts your system stability at risk.
Seasoned hackers are well aware of software vulnerabilities, and unpatched programs invite them to infiltrate your network. Don’t let them in through the back door.
Ensure you have an effective patch management strategy to stay ahead of threats and fortify your own devices with the latest defences.
11. Require Security Training
Regular security training for your employees is a must. It’s crucial to remind your team members of corporate network best practices, security policies, and mobile device guidelines periodically.
When new hires come on board, ensure they receive comprehensive training on mobile device management policies and safety protocols as part of their orientation.
Keep your training programs agile and up to date, especially when you implement a new MDM solution or make significant policy changes.
12. Regularly Remind Employees of Best Practices
Once your employees grasp your MDM policies, regularly reinforcing that knowledge for optimal results is essential.
Incorporate MDM guidelines into new employee orientation sessions and company manuals to ensure consistent understanding and adherence.
Expect your policies to evolve as technology advances and security measures improve. Regularly review your MDM policies, and don’t forget to remind or retrain employees whenever updates are necessary.
Safeguard Your Mobile Devices with Wingman Solutions!
In today’s BYOD era, ensuring effective mobile device management is crucial for safeguarding sensitive company data. Wingman Solutions provides intuitive, streamlined mobile device management solutions that can empower your workforce while minimizing risk.
From enforcing strong security policies to automating time-consuming tasks, Wingman Solutions has you covered. With comprehensive device management capabilities and a commitment to staying ahead of evolving threats, Wingman Solutions is your trusted ally in protecting your mobile ecosystem.




